How to Install Maxmind Geoip module for Litespeed
Previously I wrote a document that how to install Maxmind module for Apache web server.
Also I wrote how to block requests from countries wherever you want.
After four years I think you might need to this for litespeed because lots of hosting companies use that.
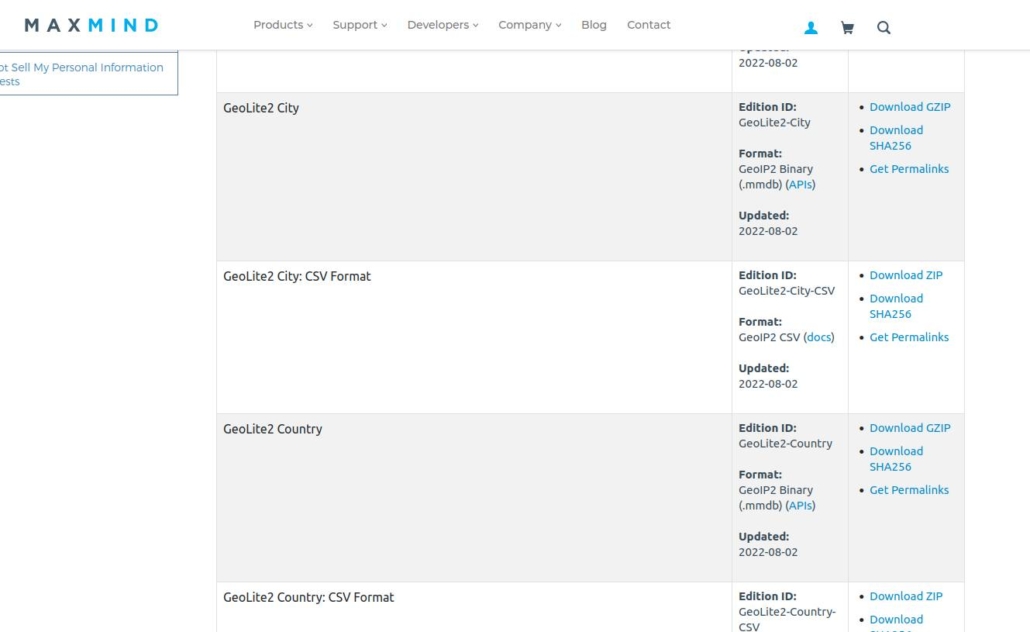
First of all,before install,you need same thing :the maxmind country ip database here (You should login first to https://www.maxmind.com
First create a folder named GeoIP under /usr/local/share/
Download the gzip or tarball and extract to /usr/local/share/GeoIP/GeoLite2-Country.mmdb<–sample name.we will use this path in litespeed admin console.
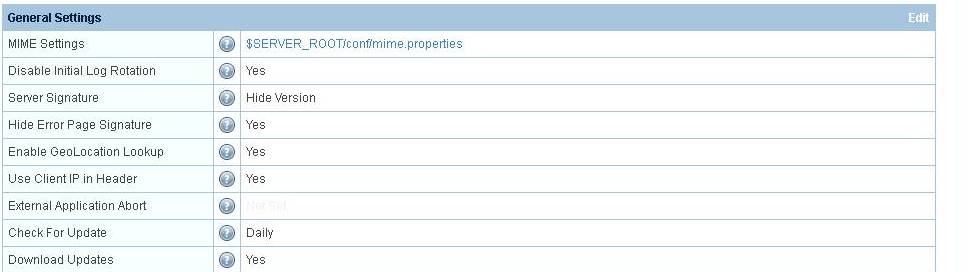
After login to your litespeed admin console->Configuration->Server
In general tab,you will see geoip lookup setting.So you enable it.
And find the details of maxmind settings section
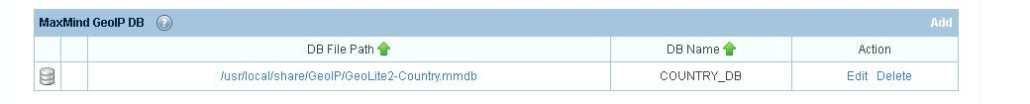
You see this is already configured.Yours will be empty.Ignore that.So you need to add some details like below;

File path must be true.DB name is really important and variable section is mandatory field.it is better to set as is.and save.Restart the litespeed server.
After you do that You verify it is installed correctly.Therefore you must see geoip variable in phpinfo page.So you upload a php file that includes phpinfo and load it from your browser.![]()
If you see that server variable then you can create some rules about deny some requests;
Assume you use Centos or Cloudlinux,go to /etc/httpd/conf.d and create a file named maxmind.conf (name is optional but it should ends with .conf)
maxmind.conf
<IfModule LiteSpeed>
GeoIPEnable On
</IfModule><IfModule mod_geoip.c>
<FilesMatch “wp-login.php|xmlrpc.php”>
SetEnvIf GEOIP_COUNTRY_CODE ^(US) AllowCountry
######Deny from env=BlockCountry
Allow from env=AllowCountry
Deny from All</FilesMatch>
<LocationMatch “^/”>
SetEnvIf GEOIP_COUNTRY_CODE ^(US) AllowCountry
######Deny from env=BlockCountry
Allow from env=AllowCountry
Deny from All</LocationMatch>
<LocationMatch “^/admin”>
SetEnvIf GEOIP_COUNTRY_CODE ^(US) AllowCountry
######Deny from env=BlockCountry
Allow from env=AllowCountry
Deny from All</LocationMatch>
<LocationMatch “^/wp-admin”>
SetEnvIf GEOIP_COUNTRY_CODE ^(US) AllowCountry
######Deny from env=BlockCountry
Allow from env=AllowCountry
Deny from All</LocationMatch>
</IfModule>
1.First section enables the geoip lookup
2.Filesmatch directive matches request to your spesific file name regardless of where.So it can be / or /abc.
3.Locationmatch is a folder generally
So according to these directives Accessing outside of US to your site root /,/admin and /wp-admin will be blocked as well as wp-login.php and xmlrpc.php
You can allow multiple country by adding their iso codes with this syntax (I guess)
SetEnvIf GEOIP_COUNTRY_CODE ^(US|FR|DE) AllowCountry
After you finish your configuration file,save it and restart litespeed.
To verify,Opera browser or open proxies will help you.

 Linux Support Here
Linux Support Here